Retired Techie
Getting older, not necessarily wiser!
Basic LAMP Server Part 3
Published on April 13, 2023 at 7:20 am by LEWIntroduction
The server is running and a basic firewall is up. Now it is time to turn our attention towards some of the programs running on our server. In this post we will be looking at a few things you can do to program configurations to help harden your server.
Note that the items discussed here are applicable to Debian based LAMP servers.They may or may not apply to other Linux distributions. I am also assuming you are working on an unmodified system. If you have made changes to configuration files already, you will need to extrapolate the below to your file structure.
Admittedly some of this stuff is security by obfuscation. So it will not deter a your more determined hackers. But it will slow down and possibly stop the casual hacker.
Apache Configuration
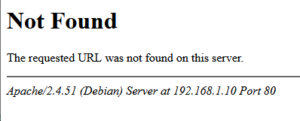
One of the things that the Apache web server does is announce itself, especially on error pages. We do not want to help the would be hacker by providing them with any useful information, like the version number and name of your web server. Note how in the below example, Apache2 not only tells us the version, but also the operating system.
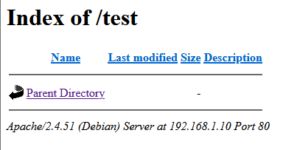
Another interesting default configuration is the ability to get a directory listing by entering a folder without any sort of index file. Something else we probably want to prevent.
Before getting to resolving these issues, we need to have a short discussion about how Debian handles the Apache2 configuration file. The actual Debian Apache2 configuration file is located at /etc/apache2/apache.conf. This file contains a series of includes to sub directories that house the actual configurations. This is why there are multiple different configuration files listed below, instead of just one.
Lets resolve the Apache identification issue. To do this on a Debian 11 system, we need to edit the /etc/apache2/config-avalible/security.conf file. We are interested in two variables that can be set in this file; ServerTokens and ServerSignature.
The ServerToken will have several entries with all but one commented out with a “#”. On a Debian System by default the “ServerTokens OS” is active. We need to deactivate this with a leading “#”, and add a new active line; “ServerTokens Prod”.
The ServerSiganture will have two options, On and Off. We want to make the Off option the active one.
Next lets fix the directory listing issue. On the Debian system we need to work with the file /etc/apache2/sites-available/000-default.conf. We need to add the following three lines under the DocumentRoot line.
<Directory var/www/html>
Options -Indexes
</Directory>
Obfuscation
I am not covering it here, but another approach that is not to hard is security through obfuscation. This involves using non standard port numbers. While this may slow down the casual user, it is not much of a deterrent to professional hackers. For example you could do ssh on port 2222 instead of 22. You just need to remember what ports you are using.
Conclusion
In this post we have covered a few basic things that can be none to help avoid other poking around on your server. Not a complete list by far, but a start. A more complete rundown on server security is the subject for another string of posts.
Because this series of posts is focused on getting a serve up and running, I have not discussed setting up and configuring virtual hosts or enabling HTTPS. These are subjects for another day.
Basic LAMP Server Part 3

Add New Comment